Uniswap V4 hooks is an area full of potential, but also threats lurking for unprepared hook developers. To innovate, they need help and tools to stay secure.
Uniswap V4 hooks
Uniswap V4 marks a significant leap in decentralized finance (DeFi). At its core, this upgrade introduces an innovative feature: hooks. These hooks are set to transform how transactions are conducted in liquidity pools and asset swaps, redefining interaction norms within the DeFi ecosystem.
By integrating hooks, Uniswap V4 allows for more flexible and functional operations in liquidity pools. However, greater freedom comes with a price of greater risk.
We identified a large number of threats during the research described in this article.
This time, we will focus on the current state and the ideas on how to change it by further research.
Current state
The concept of Uniswap V4 hooks, being relatively new and still explored, presents a landscape where developers currently face a scarcity of comprehensive resources whom they can fully trust.
There's a significant effort underway to enrich this domain. The Uniswap Foundation, alongside us and other recipients of its grants, is actively engaged in creating quality resources to let builders innovate in a secure manner. As a result, while resources may be initially limited, there are a few worth mentioning as they can significantly boost developers' understanding, security awareness, and application of hooks in Uniswap V4.
Let's take a look at what has already been created besides official documentation and how it will be useful for you as a developer.
Open Source Directory for Uniswap V4 Hooks
A collection of hooks, specifically tailored for Uniswap v4, gathered and curated by the community. At the time of writing this article, there are 99 hooks there (mainly from ETHGlobal NYC and from Community), and probably even more now.
A great place to conveniently find implementations similar to your intended use case.
Uniswap V4 by example
We all know solidity-by-example very well, the concept here is very similar. The website contains a set of simple examples that will gradually cover more and more complex applications. It is currently divided into 3 main categories: lifecycle, hooks, and transaction fees.
In the future, it may display more popular snippets to highlight other features.
Uniswap V4 Hooks Guide
Guide aimed at giving an understanding of Uniswap v4 features and implementation patterns in a very friendly way. It provides a step-by-step walkthrough of the development of three hooks with Captain Hook.
If you're a pirate, you know where to start. Arrr!
Builders Perspective on UniV4 hooks
An article that perfectly shows what design choices and possibilities you face from a developer's perspective. The Brokkr Finance team uses the example of the Locking Liquidity Hook to present the thought process and decisions made that result in a POC smart contract.
As part of the grant, further examples will be created on their blog.
Threat modeling for Uniswap v4 hooks

Our article, examines in great detail the threats resulting from the opportunities offered by individual hook use cases. We analyzed 7 selected types of hooks including: Median Oracle, Multi-sig, KYC, Hedge, Limit order, Locking liquidity, and Dynamic fees.
The article contains an extensive list of threats that you should be aware of when designing your own hook.
SCSVS C9: Uniswap v4 hook
The Smart Contract Security Verification Standard is the most comprehensive existing standard for DApps builders and auditors. As part of the grant, we created a new category dedicated to Uniswap v4 hooks. It contains a checklist that you can use by adding it to your internal knowledge base.
Share it with your team to create best security practices or support threat modeling sessions.
Static hook analyzer
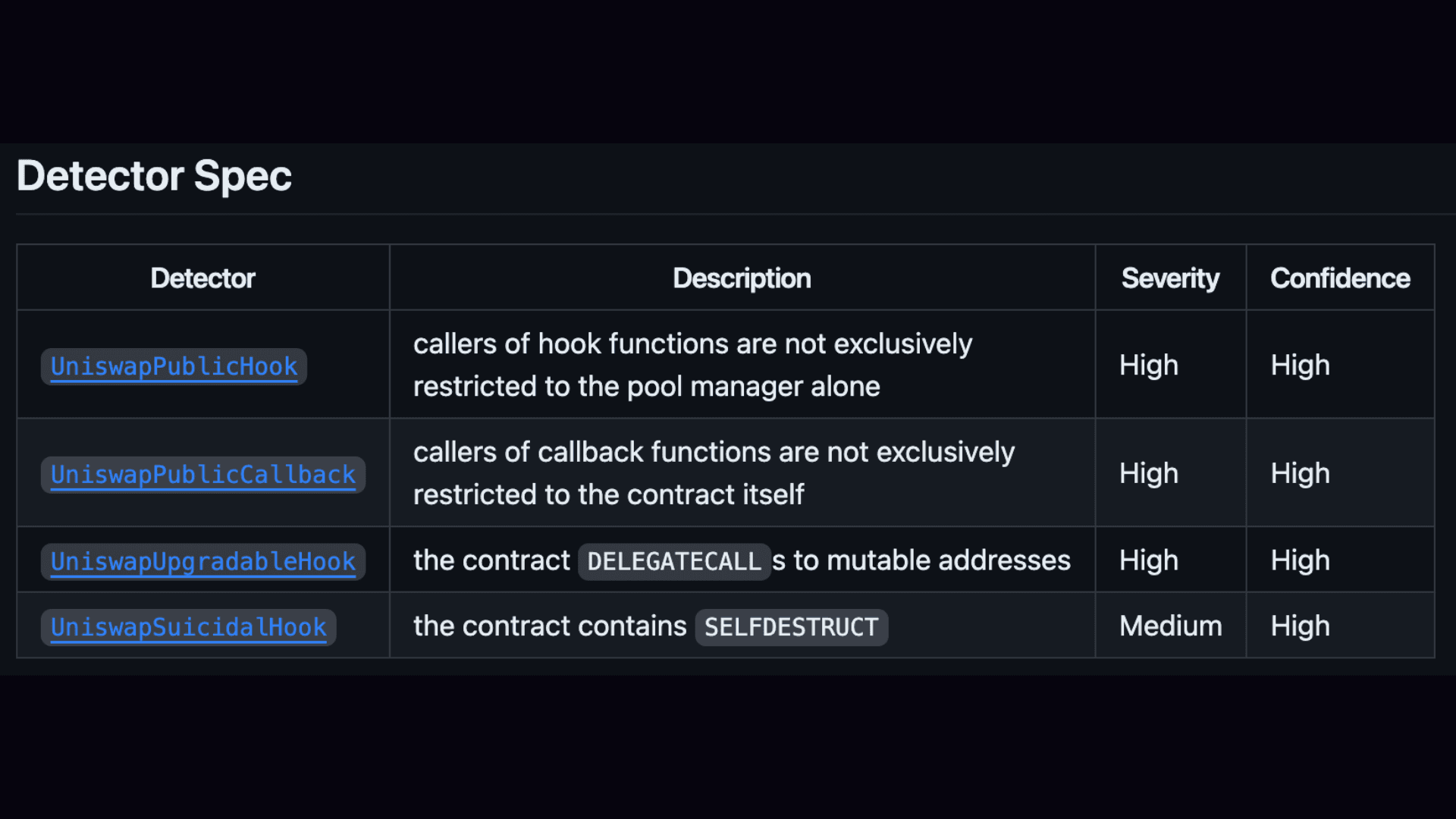
As part of the grant, the BlockSec team created a static analyzer to detect some of the vulnerabilities. The HookScan can be integrated into the SCDLC to scan Uniswap v4 hooks and cover basic threats automatically. To thoroughly secure your smart contracts, consider a smart contract audit.
There is a need for more
Although some materials have been created, with the exception of threat modeling, static analyzer, and checklist. They are largely focused on helping you explore and understand the potential of hooks and how to get started.
This is innovation-oriented thinking, but without strict security, it will be fragile.
Ideas for further research, products, and services
So what can be done to make innovation happen quickly, efficiently, and at the same time remain antifragile?
We can contribute, we can share security awareness, and we can equip developers with the tools they need. Some good existing solutions need to be reused and adapted. Several new ones should be created because this landscape has very concrete and specific needs.
Why is security so important? Although the most important thing is always the user's safety and fair behavior, there is something else.
Security is nothing more than high quality, and high quality is what we all expect from solutions built on-chain.
Let's get to the ideas.
Hook wizard
Main goal: To boost the adoption and reuse of proven, audited code by providing developers with access to tools to easily create secure, standardized hooks.
Idea description: The "Hook Wizard" concept (similar to the OpenZeppelin Wizard functionality), is designed to help developers quickly generate hooks based on well-tested and audited implementations. This tool would offer limited customization, ensuring a high level of trust in the resulting code. Through a user-friendly GUI, developers can select desired features, and the tool would produce a nearly complete hook implementation, requiring only minor parameter adjustments.
Advantages
- Ensures security and reliability by reusing code that has been thoroughly audited.
- Lowers the technical barrier to entry, making it easier for a broader audience to create hooks.
- Promotes the use of industry-standard practices in smart contract development.
Challenges
- Ensuring the tool includes only the most secure and appropriate implementations is crucial.
- The limited customization might not meet all developers' needs, potentially restricting innovation.
- Regular updates are essential to keep the tool relevant and secure.
Automated Trust Scoring
Main goal: To streamline the process of approving hooks by implementing a semi-automated trust scoring system.
Idea description: This initiative involves developing a trust scoring system that categorizes hooks based on a set of predefined rules and scores. The underlying assumption is that many hooks will have similar functionalities or can be forks of existing ones. The system would start each hook with an initial score, then apply a publicly accessible checklist, assisted by tools like static analyzers and semgrep rules, to assess the hook's trustworthiness.
Key assessment criteria could include the presence of administrative functions, upgradeability, the presence of integration with external smart contracts, and more. Each criterion not met would lower the trust score. Based on the final score, hooks would be categorized into three main groups:
Category A: Simple uniswap hooks or those based on proven, accepted, and reusable implementations.
Category B: Uniswap hooks that have high scores, but don't fully pass the checklist or are not registered as reusable, recommending an external audit by a trusted partner.
Category C: Uniswap hooks failing many checks, with new implementations or containing high-risk functions, suggesting audits by multiple trusted partners, or undergoing a separate justification process.
This categorization is designed to expedite the approval of simple hooks and enhance the reusability of trusted hooks, acknowledging that some complex hooks, while secure in certain contexts, might not be universally reusable. The whole thing can be imagined in the form of and function of a DAO that has separate flows for different proposals.
Advantages
- Facilitates quicker acceptance and deployment of simple, low-risk hooks.
- Encourages the use of hooks that are already vetted and considered reliable.
- Provides a structured and transparent way to assess the security of hooks.
Challenges
- Creating a checklist that accurately reflects security standards and allows for meaningful categorization is complex.
- Ensuring the system is rigorous enough to maintain security while being accessible and practical for developers.
- The system must be flexible to adapt to new security threats and evolving best practices in smart contract development.
- There's a potential risk that developers might rely too much on the scoring system, overlooking the nuances and specific context of their implementations.
Hook registry
Main goal: To help users make informed choices, and manage risks and security by providing an accessible and comprehensive dashboard with information about hooks used in liquidity pools.
Idea description: Building on the Trust Scoring system concept from the previous paragraph, the idea is to create an on-chain smart contract registry that stores detailed information about hooks. This registry would include data such as trust scores, categories, names and signatures of trusted partners, and hook contract creators. With this information readily available on-chain, it becomes feasible to develop user-friendly dashboards, similar to platforms like L2BEAT but tailored for Uniswap V4 hooks. These dashboards would display the hook used in each pool along with their trust levels. Users would be able to filter pools based on preferences such as trusted partners or hook creators, enabling them to make more informed and secure choices.
Advantages
- Increases transparency regarding the security and trustworthiness of hooks in different pools.
- Dashboards would offer a user-friendly interface for users to assess and compare different pools based on their security features.
- Allows users to personalize their pool selections based on specific criteria, such as preferred trusted partners or hook creators.
Challenges
- Crafting a smart contract standard that effectively captures and communicates all relevant information for users is complex.
- Creating dashboards that are informative, easy to navigate, and equipped with appropriate filters.
Hook security extensions
Main goal: Minimizing threats through pre-built security mechanisms.
Idea description: This concept proposes the creation of abstracts that hooks can inherit, equipped with predefined security mechanisms or invariants. These abstracts would embed essential security features directly into the hooks. Examples of such abstracts could include MaxSlippage, LiquidityValidation, PriceImpactLimit. By incorporating these abstracts, hooks can automatically integrate predefined security measures.
Advantages
- Inheritance from such abstracts improves the security of hooks against common vulnerabilities.
- Using predefined abstracts helps standardize security practices across different hooks.
- Ready-made, standardized security elements simplify the process of trust scoring for hooks.
Challenges
- Crafting abstracts that are both effective in security terms and efficient in performance is challenging.
- Creating abstracts that are versatile enough to be applicable across a wide range of use cases and scenarios.
- Keeping the abstracts updated with the latest security practices and responding to new types of threats.
Hook educational CTF
Main goal: To educate developers on smart contract security through engaging, gamified challenges and examples.
Idea description: Inspired by platforms like DamnVulnerableDeFi and Ethernaut, this concept involves creating an educational Capture The Flag (CTF) program focused on smart contract hooks. The CTF would feature a series of intentionally flawed hooks, known as "Bad Hooks," along with their corresponding proofs of concept (PoCs) for exploitation.
Developers participating in the CTF would have the task of exploiting these vulnerabilities to make specific tests pass. This hands-on, interactive approach aims to provide a deep understanding of threats in hooks and effective strategies to identify and mitigate them.
Advantages
- Offers a hands-on approach to learning about threats.
- Utilizes already developed by us "Bad Hooks" and PoCs, making it relatively simple to set up.
Challenges
- Creating tasks that are both educational and engaging for a wide range of skill levels.
- Attracting a wide range of participants to the CTF and maintaining their interest over time.
General fuzzing suite for hooks
Main goal: Create a reusable fuzzing test suite with minimal customization required.
Idea description: Acknowledging the critical role of testing in smart contract security, this idea involves creating a general-purpose fuzzing suite tailored for hooks. Developers are now diligently writing test suites to achieve 100% coverage in their projects. Yet, achieving this coverage is just the starting point. It's beneficial to support these tests with fuzzing. This suite would provide a standardized template for integrating fuzzing into the testing workflow, simplifying the process for developers.
The goal is to make fuzzing a more common practice in smart contract development, enhancing the early detection of vulnerabilities and thereby improving the overall security of the ecosystem.
Advantages
- Fuzzing provides a deeper level of testing, uncovering vulnerabilities that might be missed in standard tests.
- Helps in identifying vulnerabilities internally at an early development stage.
Challenges
- Developing a fuzzing suite that is sufficiently general to be applicable across a wide range of hooks and use cases.
- Keeping the suite updated with the latest testing methodologies and adapting to new types of smart contract vulnerabilities.
- Convincing developers to adopt this new tool and integrate it into their existing development processes.
Front-end simulations
Main goal: Provide users with a clear, intuitive understanding of how their actions would affect their assets and investments
Idea description: A front-end interface that simulates transaction executions. This simulation could display to users the results and performance evaluations of the pools or hooks they are considering, offering clear and interactive insights into their potential transactions.
Advantages
- A clearer view of the potential outcomes of user transactions.
- Empowers users by providing them with the same level of information and predictive capabilities that are usually reserved for more advanced or professional users.
Challenges
- Comprehensive and easy-to-read presentation of results.
- There's a risk that users might misinterpret the data or rely too heavily on simulations for decision-making, leading to potential financial mistakes.
Expansions of SCSVS hook category
Main goal: Enhance the security framework by identifying and mitigating a broader range of potential vulnerabilities specific to smart contract hooks.
Idea description: The proposed expansion involves a thorough analysis and integration of new threat scenarios into the SCSVS hook category. By systematically identifying potential threats and vulnerabilities that were not previously covered, this initiative seeks to update and enrich the standard.
It would involve collaboration with security experts, developers, and researchers to gather insights on emerging risks and effective countermeasures. This process would result in a more robust and comprehensive set of guidelines and best practices for securing smart contract hooks.
Advantages
- By addressing a wider array of threats, the standard becomes more robust, reducing the risk of vulnerabilities in smart contracts.
- A more comprehensive standard can increase trust among users, knowing that the contracts adhere to stringent security measures.
- This expansion serves as a valuable knowledge base, disseminating information about new threats and defense mechanisms within the community.
Challenges
- There is a need to balance making the standard comprehensive against keeping it practical and implementable for developers of varying skill levels.
- Adding too many threats might make the standard overly complex, making it difficult for developers to effectively implement it.
- The fast-evolving nature of blockchain technology and smart contract development means new threats are constantly emerging, making it challenging to keep the standard updated.
PoolOperator by Uniswap
Main goal: This initiative focuses on promoting pools and hooks that are audited, comply with standard protocol implementations, and adhere to established security guidelines.
Idea description: "PoolOperator by Uniswap" would involve creating a framework for evaluating and approving liquidity pools and hooks. This would include a set of criteria liquidity pools and hooks must meet to be whitelisted, such as undergoing thorough audits and adhering to best practices in smart contract development. The idea is to create a trusted ecosystem within Uniswap where users can engage with pools and hooks that are verified for security and reliability.
Advantages
- Users can interact with whitelisted pools and hooks with confidence, knowing they have passed stringent security checks.
- Encourages developers to follow standard implementations and security protocols, fostering a culture of excellence.
Challenges
- Scaling this approach is challenging.
- Risk of centralizing power in the hands of those who control the whitelisting process.
- New and innovative pools or hooks might face difficulties in getting whitelisted, especially if they deviate from standard practices in a beneficial way
Keeping the whitelisting criteria up-to-date with evolving standards and practices in the fast-paced DeFi space is a continuous challenge.
Uniswap v4 hook security research summary
The ideas we've discussed, ranging from automated trust scoring systems and hook registries to educational CTFs and general fuzzing suites, each contribute uniquely towards one goal. They collectively aim to elevate the standards of smart contract security, simplify the development process, and empower both developers and users with more information and capabilities.
The overarching theme is clear: a focus on security, efficiency, and accessibility.
These ideas represent just a fraction of the potential innovations in this space. There's a vast scope for additional ones further pushing the boundaries of what's possible in this rapidly evolving ecosystem.
Let's hear what other people involved in the development of Uniswap V4 hooks think about it
A few takes from other experts
saucepoint Outside of hook functions, one area of security research and tooling I’m very stoked on is custom curves. Custom accounting turns Uniswap v4 into a universal AMM interface, where swap math and liquidity exist beyond the core v4 code. Much like hooks, the developer's flexibility on curves creates bountiful footguns and means of getting rekt.
randomiser We have similar thoughts. In particular, the Hook registry and PoolOperator by Uniswap could be practical ways to promote and publicize "secure" hooks.
Tyllen Uniswap V4 opens up a wide gamut of security considerations when developing hooks on top of the protocol. As application or protocol developers, understanding how to build a successful hook that is secure and consistent will be very important in the adoption of the hook by other developers and usage by Liquidity Providers. It’s by doing more research and by helping developers with Uniswap V4 Hooks that we can make this possible.
Uniswap V4 hooks security future
The diversity of these ideas highlights the multifaceted challenges and opportunities present in this new hook landscape. Their prioritization is key to effective resource allocation and achieving impactful results. Factors like ease of implementation and potential benefits are crucial in determining which of them to pursue. For instance, solutions that are simpler to implement might be prioritized to provide immediate enhancements in security, while more complex projects with long-term benefits could form the basis of ongoing research and development efforts.
Other considerations for prioritization may include the scalability of the solution, the extent of its impact on user experience, and its ability to address current and anticipated security challenges. Balancing these factors ensures that the initiatives undertaken not only advance the field of hook security but also contribute positively to the security efforts of the broader DeFi ecosystem.
Collaboration involving developers and security experts plays a crucial role in this.
- Do you want to discuss hook smart contract security with us? Let's talk!
Composable Security 🇵🇱⛓️ is a company founded by the authors of the Smart Contract Security Verification Standard focused on a comprehensive approach to the security of decentralized protocols. We specialize in smart contract audits of projects written in Solidity. Examples of projects that have trusted us are market leaders such as FujiDAO, Enjin, Volmex Finance, DIVA Protocol, and Tellor. Read more about us here
About the author
Co-author of SCSVS and White Hat. Professionally dealing with security since 2017 and since 2019 contributing to the crypto space. Big DeFi fan and smart contract security researcher.